SHA3-512: A Developer’s Guide to Secure Data Storage and Verification
Cryptographic hash functions are essential tools used for securing data integrity and authenticity. One such hash function is the Secure Hash Algorithm 3 (SHA-3), a family of cryptographically secure hash functions designed by the US National Security Agency (NSA). The SHA3_512 hash function is one of the members of the SHA-3 family and can generate a fixed-length 512-bit output from input data of any size. In this article, we’ll explore SHA3_512 Hash and how developers can use it for secure data hashing.
How SHA3_512 Hash Works
The SHA3_512 hash algorithm works by taking an input message and processing it through multiple rounds of computations that produce a fixed-length hash value as output. This output value, known as a message digest, has several important properties, including:
- It is unique for any given input message
- Any modification made to the input message will result in a completely different digest
- It is computationally infeasible to generate an input message from the message digest
The SHA3_512 Hash algorithm was designed to counteract security vulnerabilities inherent in earlier hash functions, such as SHA-1 and SHA-2. This function uses a sponge function design that utilizes Permutation-Based Hashing in its internal workings. The input data is first padded and sliced before undergoing Keccak-f function processing that shuffles and replaces the state of the hash function in each round until it produces the final hash output of a fixed length.
Sample Code
Developers can use SHA3_512 Hash algorithm in various programming languages such as C++, Java, Python, and more. Here’s a Python example of how to create hash functions using the hashlib module in Python:
import hashlib
str_data = b'The quick brown fox jumps over the lazy dog'
# Creating sha3 hash object
sha3_obj = hashlib.sha3_512(str_data)
# Getting hash
hash_value = sha3_obj.hexdigest()
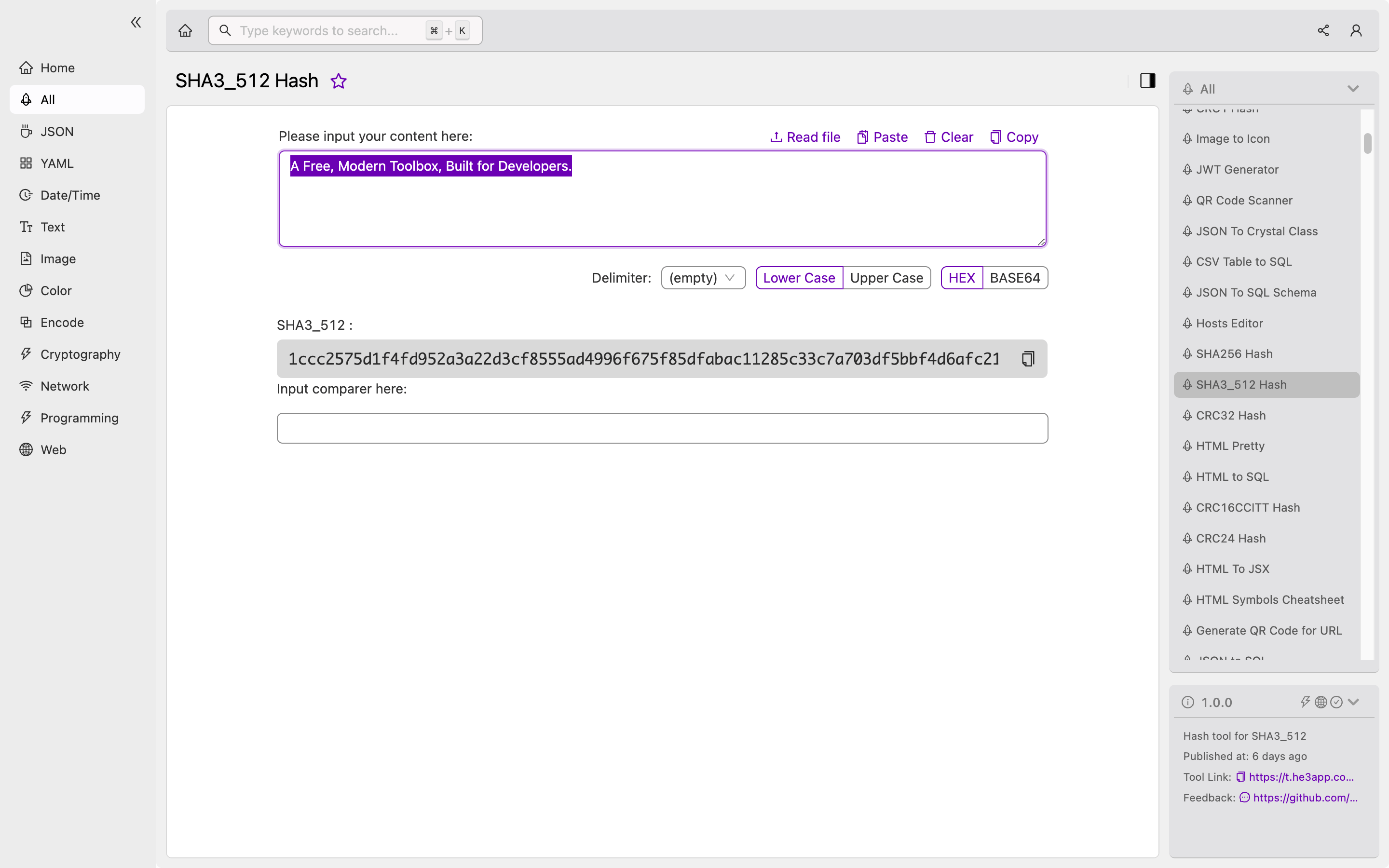
print("SHA3_512 Hash of the given data is: ", hash_value)Or you can use SHA3_512 Hash tool in He3 Toolbox (https://t.he3app.com?p2ig ) easily.
Scenarios of Using SHA3_512 Hash
The SHA3_512 hash algorithm can be useful for a wide range of applications that require data integrity and security, including:
- Password storage and verification
- Digital signatures (e.g., in blockchain applications)
- Cryptography key generation
- Data backup and recovery
- File sharing and network communication
Key Features of SHA3_512 Hash
Here are some key features of the SHA3_512 hash algorithm that make it a popular choice for data hash functions:
- Large hash output size (512 bits)
- High cryptographic strength and resistance to brute force attacks
- Good performance in both hardware and software implementations
- Security against birthday attacks and other cryptographic weaknesses
- Support for multiple hashing modes and padding schemes
Misconceptions about SHA3_512 Hash
There can be several misconceptions about the SHA3_512 Hash algorithm, including:
- It provides encryption rather than just hashing (untrue)
- It has a fixed output size of 512 bytes (true)
- It is vulnerable to quantum computing attacks (unknown, as it hasn’t been tested on a quantum computer yet)
FAQs
-
Is SHA3_512 Hash function secure enough for data integrity verification? Ans: Yes, SHA3_512 hash function is widely considered to be one of the most secure hash functions, thanks to its large output size, sponge-based design, and resistance to various cryptographic attacks.
-
Can SHA3_512 Hash function be used for password storage and verification? Ans: Yes, SHA3_512 hash function can be used for password storage and verification, but it is recommended to include additional security measures like salting and stretching for stronger protection against brute force attacks.
Conclusion
In summary, the SHA3_512 Hash algorithm is a valuable cryptographic tool for developers who want to ensure the integrity and security of their data. By understanding its workings and features, developers can use this hash function in various scenarios that require secure and robust data hashing.
References:
