Understanding SHA3_224 Hash for Developers
Security is paramount in today’s digital world, and developers need to ensure that their applications are secure. This is where SHA3_224 Hash comes in. In this article, we will explain what SHA3_224 Hash is, how it works, its key features, common misconceptions, and scenarios where you can use it.
What is SHA3_224 Hash?
SHA3_224 is a cryptographic hash function that generates a 224-bit hash value. It is a member of the Secure Hash Algorithm family, which includes SHA-1, SHA-2, and others. A hash function takes an input (message) and produces a fixed-size output (hash value) that represents the original message. SHA3_224 Hash is often used to verify the integrity of data, detect unauthorized changes, and password storage.
How It Works
SHA3_224 Hash uses a sponge construction named Keccak. The message is first padded to a multiple of the block size of 1152 bits. Then, the padded message is divided into blocks of the same size as the capacity of the sponge (1600 bits). An initialization vector (IV) is XORed with the first block, and the resulting state is fed into the sponge function. The output is then XORed with the IV and the next block, and the process continues until all blocks have been processed. Finally, the output is truncated to the desired length of 224 bits.
Sample Code
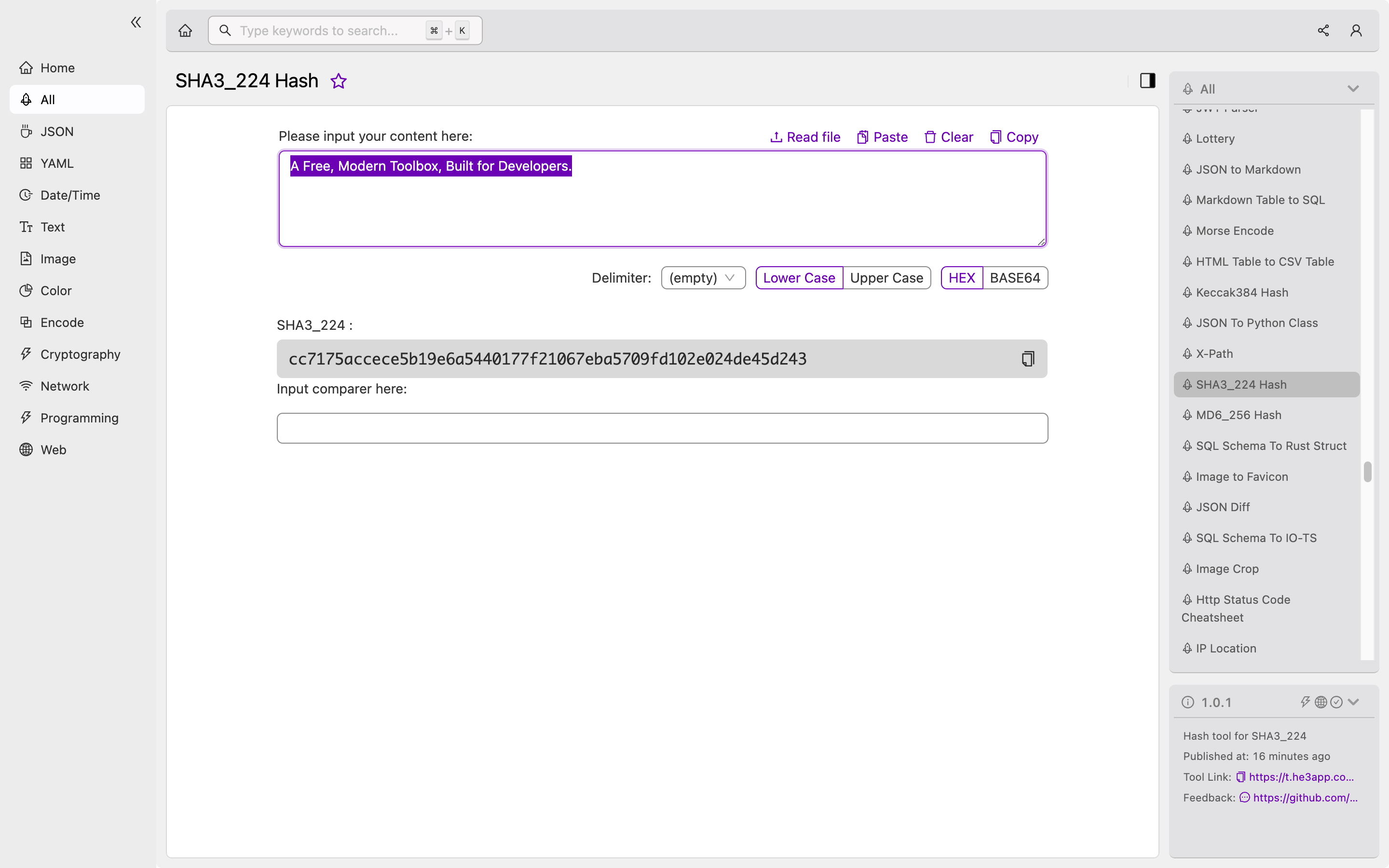
Here is an example of how to implement SHA3_224 Hash in Python:
import hashlib
message = b'This is a sample message'
hash_object = hashlib.sha3_224(message)
hex_dig = hash_object.hexdigest()
print(hex_dig)Output:
3982e3f3d1dc2b749b8cfc0a7d967f61bd56d7a1cbb20a7e6baa36bOr you can use SHA3_224 Hash tool in He3 Toolbox (https://t.he3app.com?mrtg) easily.
Key Features
Here are some key features of SHA3_224 Hash:
- Generates a fixed-size 224-bit hash value
- Uses a sponge construction named Keccak
- Retroactively standardized by NIST in 2015
- Resistant to length extension attacks
- Suitable for password storage
Scenarios for Developers
Here are some scenarios where you can use SHA3_224 Hash:
- Password storage: SHA3_224 Hash is a secure way to store passwords. When a user enters their password, it is hashed and compared with the stored hash value. This ensures that the password is correct without revealing the plain text password.
- Data integrity: SHA3_224 Hash can be used to verify that data has not been tampered with. A hash value can be calculated for a file, message, or any other data, and compared with a known hash value to detect unauthorized changes.
Misconceptions and FAQs
Is SHA3_224 Hash secure?
Yes, SHA3_224 Hash is secure. It is a member of the Secure Hash Algorithm family and has been designed to be resistant to attacks. However, like any other encryption method, there is always a risk of being compromised if a flaw is discovered.
Can SHA3_224 Hash be decrypted?
No, SHA3_224 Hash is a one-way function. It cannot be decrypted, and the original message cannot be recovered from the hash value.
Conclusion
In summary, SHA3_224 Hash is a cryptographic hash function that generates a fixed-size 224-bit hash value. It is used to verify data integrity, detect unauthorized changes, and store passwords. SHA3_224 Hash is secure, and its key features make it suitable for various scenarios. As a developer, understanding SHA3_224 Hash is essential to ensure the security of your applications.
References:
