Understanding SHA384 Hash for Developers
In today’s digital world, data security is of utmost importance. Encryption is a popular method of securing data, and hashing algorithms play an important role in encrypting data. SHA384 Hash is a popular hashing algorithm that is used for data security. In this article, we will delve into the concept of SHA384 Hash and explore its features, scenarios, and misconceptions.
What is SHA384 Hash?
SHA384 Hash is a hashing algorithm that is used to generate a fixed-size, unique, and secure hash value for a given input data. The Secure Hash Algorithm (SHA) family comprises of several hashing algorithms, with SHA-384 being one of them. SHA384 Hash produces a 384-bit hash value, making it more secure than the SHA256 algorithm, which produces a 256-bit hash value.
SHA384 Hash uses a series of logical operations, such as bitwise operations, rotations, and modular arithmetic, to generate a hash value. The input data is divided into blocks of a fixed size, and each block is processed using the SHA384 algorithm. The resulting hash value is unique to the input data, and any change in the input data will result in a different hash value.
How Does SHA384 Hash Work?
SHA384 Hash works by taking a message of any length and transforming it into a fixed-length output of 384 bits. The algorithm uses a series of operations to process the input data, such as:
- Padding: The input message is padded with bits to ensure that the message is a multiple of 1024 bits.
- Message Schedule Calculation: The input message is divided into 1024-bit blocks, and the blocks are further divided into 80 64-bit words.
- Compression Function: The compression function takes a 1024-bit block of the input message and updates the intermediate hash value.
The output hash value is then generated by concatenating the final intermediate hash values. SHA384 Hash is a one-way algorithm, meaning that it is practically impossible to reverse the output hash value to retrieve the input message.
Scenarios for Using SHA384 Hash
Developers often use SHA384 Hash for various purposes, such as:
- Data Integrity Verification: SHA384 Hash is commonly used to verify the integrity of data, ensuring that the data has not been tampered with or altered.
- Password Storage: SHA384 Hash is useful for encrypting user passwords and storing them in a database. When a user logs in, the password is hashed using the SHA384 algorithm, and the resulting hash value is compared with the stored hash value.
- Digital Signatures: SHA384 Hash is used to create digital signatures that verify the authenticity and integrity of digital documents.
Features of SHA384 Hash
Here are some key features of SHA384 Hash:
| Feature | Description |
|---|---|
| Fixed Hash Length | SHA384 Hash produces a fixed-length output of 384 bits, making it more secure than SHA256. |
| Collision Resistance | SHA384 Hash is collision-resistant, meaning that it is unlikely to generate the same hash value for different input messages. |
| One-Way Algorithm | SHA384 Hash is a one-way algorithm, making it impossible to retrieve the input message from the output hash value. |
Misconceptions about SHA384 Hash
There are some misconceptions about SHA384 Hash, such as:
- SHA384 is Not Encryption: SHA384 Hash is a hashing algorithm and not an encryption algorithm. It does not encrypt the input message but generates a unique hash value for the given input message.
- SHA384 is Not Infallible: Although SHA384 Hash is a secure hashing algorithm, it is not infallible. Given enough computing power and time, it is possible to find collisions, which are two different input messages that generate the same hash value.
FAQs
Q1: Is SHA384 Hash better than SHA256?
Yes, SHA384 Hash is more secure than SHA256 because it produces a 384-bit hash value, which is harder to break than the 256-bit hash value generated by SHA256.
Q2: Can SHA384 Hash be reversed to retrieve the input message?
No, SHA384 Hash is a one-way algorithm, meaning that it cannot be reversed to retrieve the input message from the output hash value.
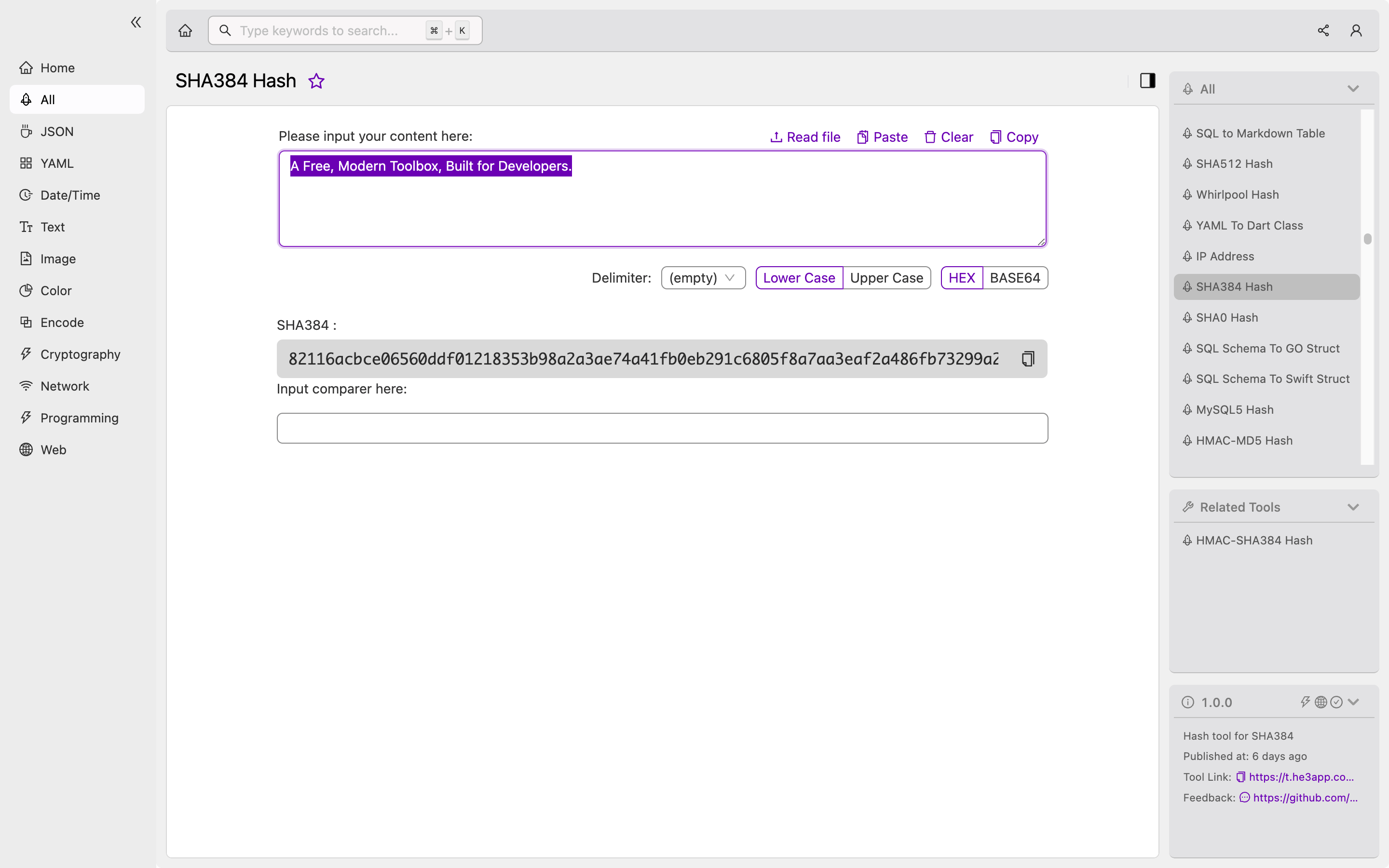
How to Use SHA384 Hash
You can use SHA384 Hash tool in He3 Toolbox (https://t.he3app.com?ir7i) easily.
Conclusion
In conclusion, SHA384 Hash is a secure and efficient hashing algorithm that plays a crucial role in data security. It is useful for various purposes such as data integrity verification, password storage, and digital signatures. Understanding the concept of SHA384 Hash, its features, and scenarios is vital for developers who want to ensure the security of their data.
References:
