Introduction
In today’s digital age, data security is of utmost importance. That’s why cryptographic hash functions like SHA1 (Secure Hash Algorithm 1) play a crucial role in keeping data safe from prying eyes. Developing and maintaining secure applications and systems requires an understanding of the underlying algorithms that ensure data privacy and integrity.
What is SHA1 Hash?
SHA1 is a cryptographic hash function used to generate a unique identifier, called a hash value or checksum, for a given input data. The function is one-way, meaning the original data cannot be derived from the hash value. This makes SHA1 particularly useful for verifying data integrity and detecting data tampering.
SHA1 Hash takes an input message of any length and produces a fixed-size output message, usually 160 bits or 20 bytes. The output message is typically represented as a hexadecimal string and is unique to the input message. Changing even a single character in the original message results in a vastly different hash value.
How Does SHA1 Hash Work?
SHA1 uses a mathematical function that operates on blocks of the input message to produce the hash value. The algorithm iteratively processes the message in 512-bit blocks until the entire message is hashed. The input block is combined with a 160-bit value called the “intermediate hash value” computed from the previous block. The algorithm then performs a series of logical operations to combine the input block and the intermediate hash value to produce a new intermediate hash value for the current block.
The final intermediate hash value is the SHA1 hash value for the entire input message. The SHA1 algorithm is designed to be computationally secure, meaning that it is extremely difficult to find a different input message that generates the same hash value.
How to Use SHA1 Hash?
Developers can use SHA1 Hash to ensure data integrity in various scenarios, such as file storage and transmission, password storage, and digital signatures. For example, when storing passwords, applications can hash the password and store the hash value in the database instead of the actual password. This way, even if the database is compromised, the attacker cannot retrieve the actual password from the hash value.
Here’s an example of how to generate the SHA1 hash of a string in Python:
import hashlib
message = "Hello, World!"
# encode the message as bytes
message_bytes = message.encode('utf-8')
# generate the SHA1 hash
sha1_hash = hashlib.sha1(message_bytes).hexdigest()
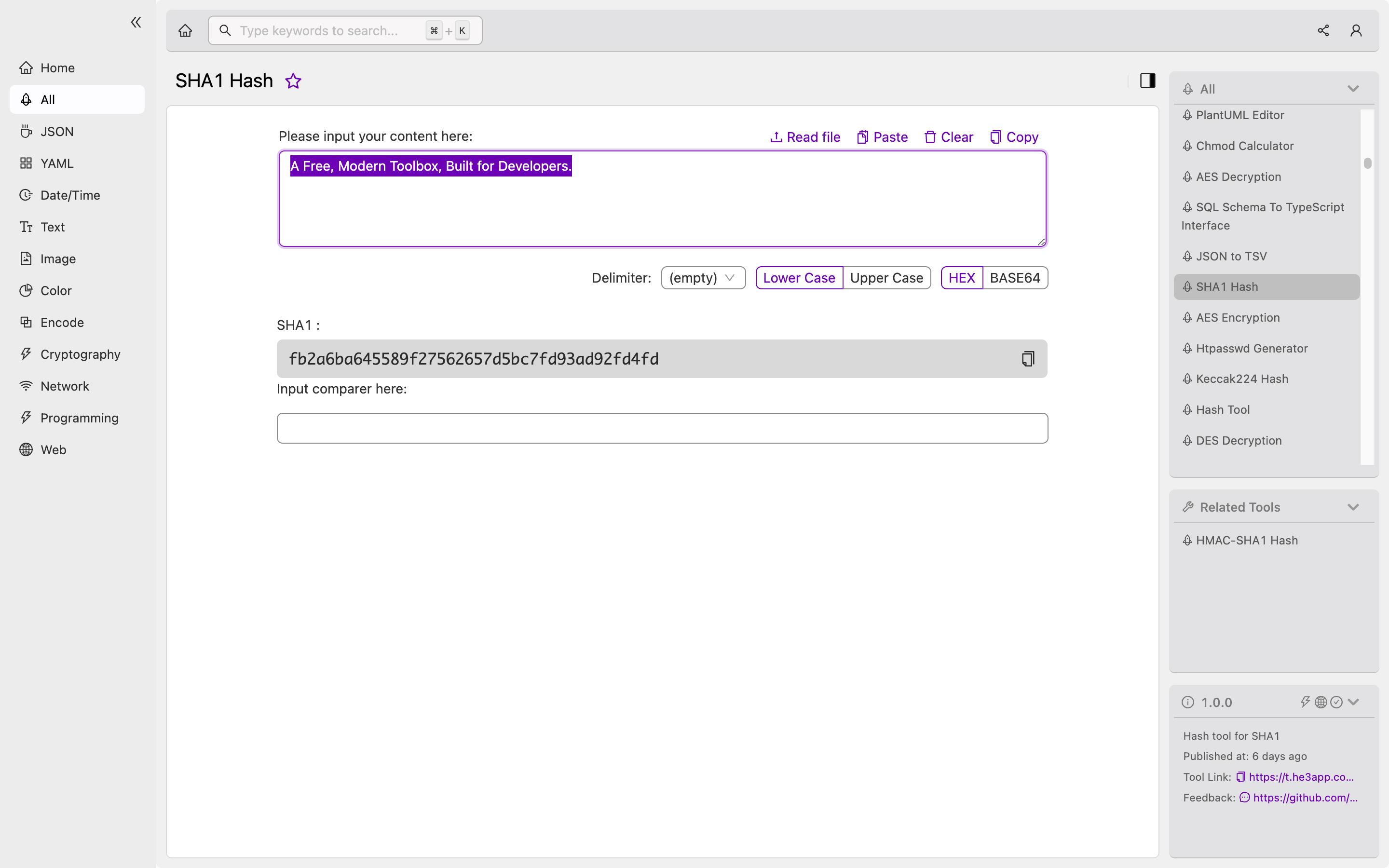
print(sha1_hash) # output: 0a4d55a8d778e5022fab701977c5d840bbc486d0Or you can use SHA1 Hash tool in He3 Toolbox (https://t.he3app.com?174s ) easily.
Key Features of SHA1 Hash
Here are some key features of the SHA1 algorithm:
-
Produces a fixed-size output message of 160 bits.
-
Is one-way, meaning the original input message cannot be derived from the hash value.
-
The hash value is unique to the input message, so any changes to the input message will result in a vastly different hash value.
-
Is designed to be computationally secure, making it very difficult to find a different input message that generates the same hash value.
-
Is widely used in various security applications to verify data integrity and detect tampering.
Misconceptions About SHA1 Hash
There are some common misconceptions about SHA1 Hash, such as:
-
SHA1 Hash provides encryption: SHA1 Hash is not an encryption algorithm, but rather a cryptographic hash function used to verify data integrity and detect tampering.
-
SHA1 Hash is unbreakable: While SHA1 Hash is designed to be computationally secure, it is not impervious to attacks. In fact, SHA1 Hash has been found to be vulnerable to collision attacks, where two different messages can produce the same hash value.
Frequently Asked Questions (FAQs)
1. Is SHA1 Hash secure?
SHA1 Hash is no longer considered secure, as it is vulnerable to collision attacks. It is recommended to use more secure hash functions like SHA-256 or SHA-3.
2. Can SHA1 Hash be reversed?
SHA1 Hash is a one-way function, meaning the original data cannot be derived from the hash value. However, given a hash value, it is possible to perform a brute-force attack to find the original data that generates the hash value.
Conclusion
In this article, we discussed the fundamentals of SHA1 Hash, how it works, and how it can be used in various scenarios to ensure data integrity and detect tampering. We also covered some misconceptions and common FAQs about the algorithm. As a developer, it’s crucial to understand the underlying principles of cryptography and hash functions to develop and maintain secure applications and systems.
References:
