Understanding Rc4 Decryption: A Guide for Developers
In the world of security and cryptography, Rc4 Decryption is a popular method used for encryption and decryption. It provides fast and efficient symmetric-key encryption, making it a go-to option for developers. In this article, we will dive into the details of Rc4 Decryption, including its concept, working process, sample code, key features, scenarios, misconceptions, and FAQs.
The Concept of Rc4 Decryption
At its core, Rc4 Decryption is a stream cipher that generates a keystream that can be used to encrypt and decrypt data. It uses a symmetric key algorithm that is shared between the sender and the receiver. The algorithm generates a random stream of bytes that is combined with the plaintext to produce ciphertext. To decrypt the data, the recipient uses the same key to generate the same keystream and then combines it with the ciphertext to produce the plaintext.
How Rc4 Decryption Works
Rc4 Decryption is a simple and fast algorithm that operates on a stream of bytes. It is based on a key-scheduling algorithm that generates a pseudorandom stream of bytes that is used to encrypt and decrypt the data. The process of generating the keystream involves swapping elements in an array based on the secret key. Once the keystream is generated, it can be XORed with the plaintext to produce the ciphertext.
Here is a sample code in Python that demonstrates how Rc4 Decryption can be used to encrypt and decrypt a message:
import ARC4
key = b'secretkey'
message = b'hello world'
cipher = ARC4.new(key)
ciphertext = cipher.encrypt(message)
print(ciphertext)
cipher = ARC4.new(key)
plaintext = cipher.decrypt(ciphertext)
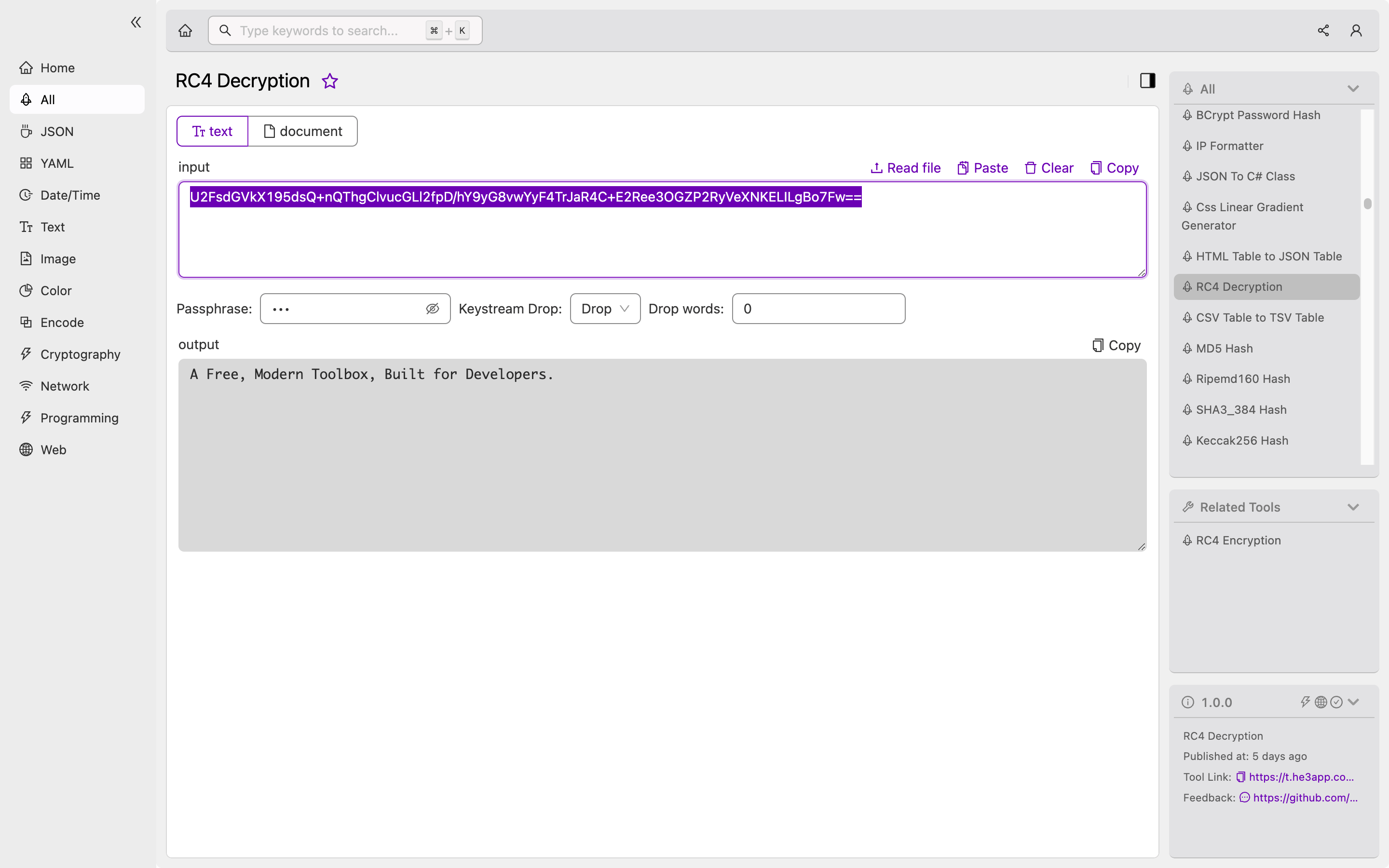
print(plaintext)Or you can use Rc4 Decryption tool in He3 Toolbox (https://t.he3app.com?b354 ) easily.
Scenarios of Rc4 Decryption for Developers
There are many scenarios where Rc4 Decryption can be a useful tool for developers. It is commonly used in applications that require fast and efficient encryption and decryption of data, such as secure communication protocols, wireless networks, and secure web browsing. It can also be used in standalone encryption and decryption applications that need to protect sensitive data.
Key Features of Rc4 Decryption
Rc4 Decryption has several key features that make it a popular encryption algorithm. These include:
- Fast and efficient encryption and decryption
- Small key size
- Easy implementation
- Widely used and supported
Misconceptions and FAQs about Rc4 Decryption
Despite its popularity as an encryption algorithm, Rc4 Decryption has been the subject of several misconceptions and FAQs. Here are two common misconceptions about Rc4 Decryption:
Misconception #1: Rc4 Decryption is Vulnerable to Attacks
There have been several known vulnerabilities with Rc4 Decryption, including key-related attacks and biases in the keystream. However, these vulnerabilities can be mitigated by using proper key management strategies and best practices.
Misconception #2: Rc4 Decryption is Outdated and Should Not Be Used
While there are newer encryption algorithms available, Rc4 Decryption is still widely used and supported in many applications. It is important to evaluate the specific requirements of your application and choose an encryption algorithm that meets those requirements.
Here are two common FAQs about Rc4 Decryption:
FAQ #1: How Can I Generate a Strong Key for Rc4 Decryption?
To generate a strong key for Rc4 Decryption, you can use a cryptographically secure random number generator to create a random key of sufficient length. It is important to use a key of at least 128 bits in length to ensure sufficient security.
FAQ #2: Can I Use Rc4 Decryption to Encrypt Large Files?
Rc4 Decryption is not well-suited for encrypting large files, as it operates on a stream of bytes and can become inefficient when dealing with large amounts of data. Instead, it is recommended to use a block cipher, such as AES, for encrypting large files.
Conclusion
Rc4 Decryption is a popular encryption algorithm that provides fast and efficient symmetric-key encryption. It is widely used in many applications that require secure communication and data protection. By understanding the concept and working process of Rc4 Decryption, developers can make informed decisions about how to use this encryption algorithm in their applications.
Reference links:
