Introduction
Cryptography plays an essential role in securing data as we rely more on digital information. One essential cryptographic tool is the message digest, which hashes data and reduces it to a fixed size. MD2 Hash is one of the earliest message digest algorithms developed, dating back to 1989. It has since been widely used in various applications, including TLS/SSL, secure email, and digital signatures. In this article, we will delve into the working of MD2 Hash and how developers can use it.
MD2 Hash Algorithm
MD2 Hash is a cryptographic hash function designed by Ronald Rivest in 1989. It uses the Merkle-Damgård construction, where the input message is divided into blocks that are processed individually. The algorithm generates a 128-bit digest of the input message, similar to other hash functions like MD5 and SHA-1.
To generate the hash, the algorithm performs the following steps:
- Padding: The input message is padded so that it is a multiple of 16 bytes.
- Initialization: The algorithm initializes eight 32-bit variables, S[0]-S[7], and sets them to a fixed value.
- Message Digest Processing: The algorithm processes each block of the message, updating the variables at each step.
- Output: After processing the entire message, the algorithm generates a 128-bit message digest.
Using MD2 Hash
Developers can use MD2 Hash to secure data in various applications. For instance, they can use it to hash passwords stored in a database, ensuring that the passwords are not stored in plain text. Developers can also use MD2 Hash to verify the integrity of a message, file, or software by comparing the computed hash with the expected hash.
MD2 Hash can be implemented in various programming languages like C, Python, and Java. Here is a sample code in Python:
import hashlib
message = "Hello World"
hash_object = hashlib.md2(message.encode())
hash_digest = hash_object.hexdigest()
print(hash_digest)This code generates the MD2 Hash of the message string and stores it in the hash_digest variable.
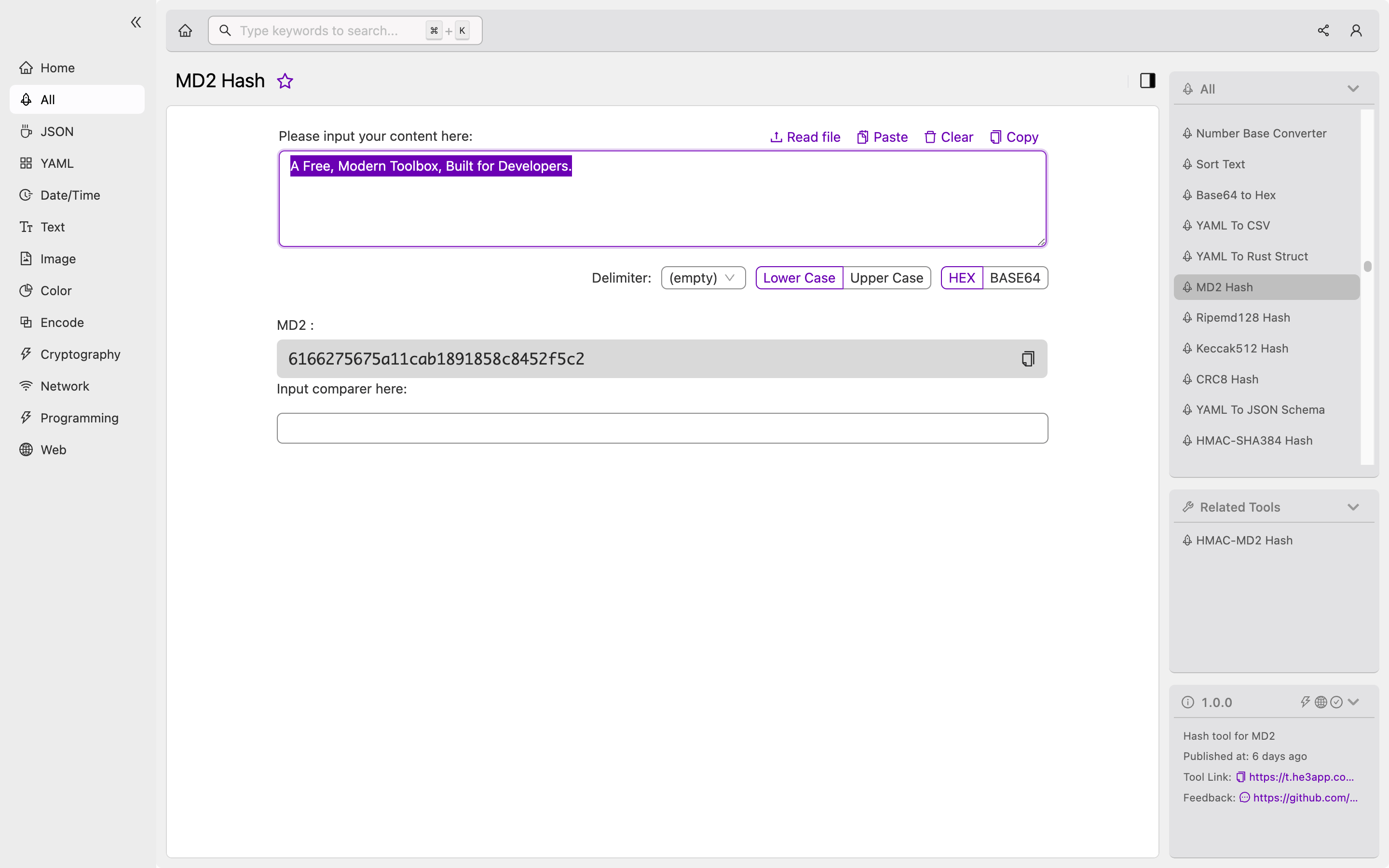
Or you can use MD2 Hash tool in He3 Toolbox (https://t.he3app.com?en97 ) easily.
Key Features
Here are some key features of MD2 Hash:
- It produces a 128-bit hash value, which is much shorter than the input message.
- The algorithm is relatively fast, making it suited for low-power devices.
- It is resistant to collision attacks, ensuring that two different messages cannot produce the same hash.
Misconceptions and FAQs
Is MD2 Hash secure?
MD2 Hash is no longer considered secure since it has several vulnerabilities, making it susceptible to attacks. Developers should use more advanced hash functions like SHA-256 and SHA-512.
Is MD2 Hash still used?
While MD2 Hash is no longer considered secure, it is still used in legacy systems and applications. However, developers should migrate to more secure hash functions.
Conclusion
MD2 Hash has been widely used in various applications, but it is no longer considered secure. Developers should choose more advanced hash functions like SHA-2 and SHA-3 for their applications. Understanding MD2 Hash is essential in cryptography, and developers should keep up with emerging technologies to keep their data secure.
References:
