Introduction
In today’s digital world, data security has become a top priority for businesses and individuals. One way to ensure data security is by using cryptographic hash functions, such as HMAC-SHA0 Hash. This article will explain what HMAC-SHA0 Hash is, how it works, its features, and misconceptions associated with it.
What is HMAC-SHA0 Hash?
HMAC-SHA0 Hash is a cryptographic hash function that uses a secret key to create a message authentication code (MAC) for data. HMAC-SHA0 Hash is a variant of HMAC (Hash-based Message Authentication Code), which is a widely used cryptographic authentication mechanism.
How does HMAC-SHA0 Hash work?
HMAC-SHA0 Hash works by taking an input message, a secret key (K), and applying the SHA0 Hash function to generate a MAC. The SHA0 Hash function generates a fixed-length, pseudo-random output called a hash value. The resulting MAC is unique to the input message and secret key. Anyone with the secret key can verify the authenticity of the data by re-generating the MAC and comparing it with the original MAC.
Here’s a sample code in Python to generate an HMAC-SHA0 Hash:
import hmac
import hashlib
key = b'secret_key'
data = b'my_data'
digest = hmac.new(key, data, hashlib.sha0).hexdigest()
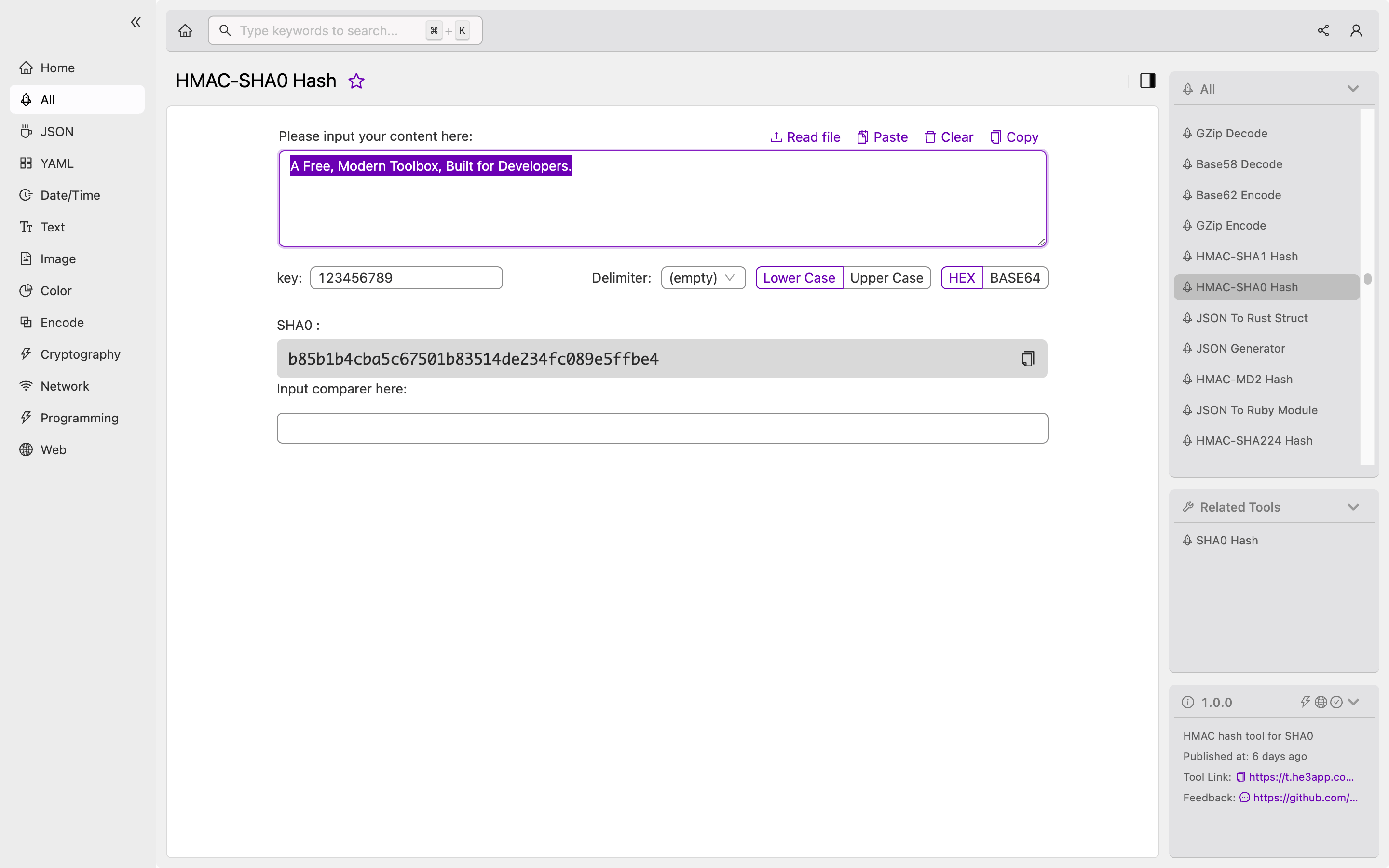
print(digest)Or you can use HMAC-SHA0 Hash tool in He3 Toolbox (https://t.he3app.com?vgzv ) easily.
Key Features
| Feature | Description |
|---|---|
| Message Integrity | HMAC-SHA0 Hash ensures that the input message has not been tampered with |
| Keyed Hashing | HMAC-SHA0 Hash uses a secret key to generate the MAC |
| Non-repudiation | HMAC-SHA0 Hash provides proof of the data’s authenticity and non-repudiation |
| Randomness | SHA0 Hash generates a pseudo-random output value that is unique to the input message |
Scenarios
Developers can use HMAC-SHA0 Hash in different scenarios, such as:
- User authentication
- Digital signatures
- Secure communication protocols
- Data integrity checks
Misconceptions
Misconception 1: HMAC-SHA0 Hash is outdated and insecure
HMAC-SHA0 Hash is an older variant of HMAC and is no longer recommended for use. Instead, the SHA-2 family of hash functions is preferred, which includes SHA-256, SHA-384, and SHA-512. However, HMAC-SHA0 Hash is still considered secure and is widely used in legacy systems.
Misconception 2: HMAC-SHA0 Hash provides encryption
HMAC-SHA0 Hash does not provide encryption but only message authentication. Encryption is a separate process where the data is transformed into an unreadable format using an encryption algorithm.
FAQs
1. Can HMAC-SHA0 Hash be decrypted?
No, HMAC-SHA0 Hash cannot be decrypted as it is a one-way function. The hash value cannot be converted back to the original input message.
2. Can HMAC-SHA0 Hash be used for password hashing?
No, HMAC-SHA0 Hash should not be used for password hashing as it is susceptible to brute-force attacks. Instead, developers should use a purpose-built password hashing function like bcrypt or Argon2.
3. Can HMAC-SHA0 Hash be used in a public key infrastructure (PKI)?
Yes, HMAC-SHA0 Hash can be used in a PKI to authenticate digital certificates.
Conclusion
HMAC-SHA0 Hash is a cryptographic hash function that provides message integrity, keyed hashing, and non-repudiation. Although it is no longer recommended for use, it is still considered secure and is widely used in legacy systems. Developers can use HMAC-SHA0 Hash for user authentication, digital signatures, secure communication protocols, and data integrity checks. To learn more about HMAC-SHA0 Hash and other cryptographic hash functions, check out the references below.
References:
