Introduction
In today’s digital world, data security, integrity, and accuracy are essential features that developers must consider when designing and developing software systems. One way to ensure data integrity and accuracy is to use hashing algorithms such as CRC8 Hash. CRC8 Hash is a cyclic redundancy check (CRC) algorithm that generates a fixed-size checksum based on a given data input. In this article, we will explore how CRC8 Hash works, its key features, misconceptions, scenarios of use, and a sample code.
How CRC8 Hash Works
CRC8 Hash is a type of CRC algorithm that applies a mathematical function to a given input data to produce a fixed-size checksum. The calculation of the CRC8 Hash involves dividing the input data into blocks of a certain size, applying a polynomial function to each block, and generating the checksum by combining the results of the polynomial operations. The resulting checksum can be used to verify the data integrity and detect errors during transmission or storage.
The polynomial function used in CRC8 Hash is represented by a binary number, which determines the type of CRC algorithm to be used. CRC8 Hash uses an 8-bit polynomial, which means that the resulting checksum has a size of 8 bits (or 1 byte).
The following is an example of the CRC8 Hash algorithm in Python:
import crcmod
# Create an instance of the CRC8 Hash algorithm
crc8_func = crcmod.predefined.mkCrcFun('crc-8')
# Calculate the CRC8 Hash of a given data input
data = b'Hello, World!'
crc8_checksum = crc8_func(data)
print(crc8_checksum)In the example above, we first import the crcmod library, which provides a set of predefined CRC functions, including the CRC8 Hash algorithm. We then create an instance of the CRC8 Hash algorithm using the mkCrcFun() function and specify the polynomial function to be used (crc-8). Finally, we calculate the CRC8 Hash of a given input data b'Hello, World!' and store the result in the variable crc8_checksum.
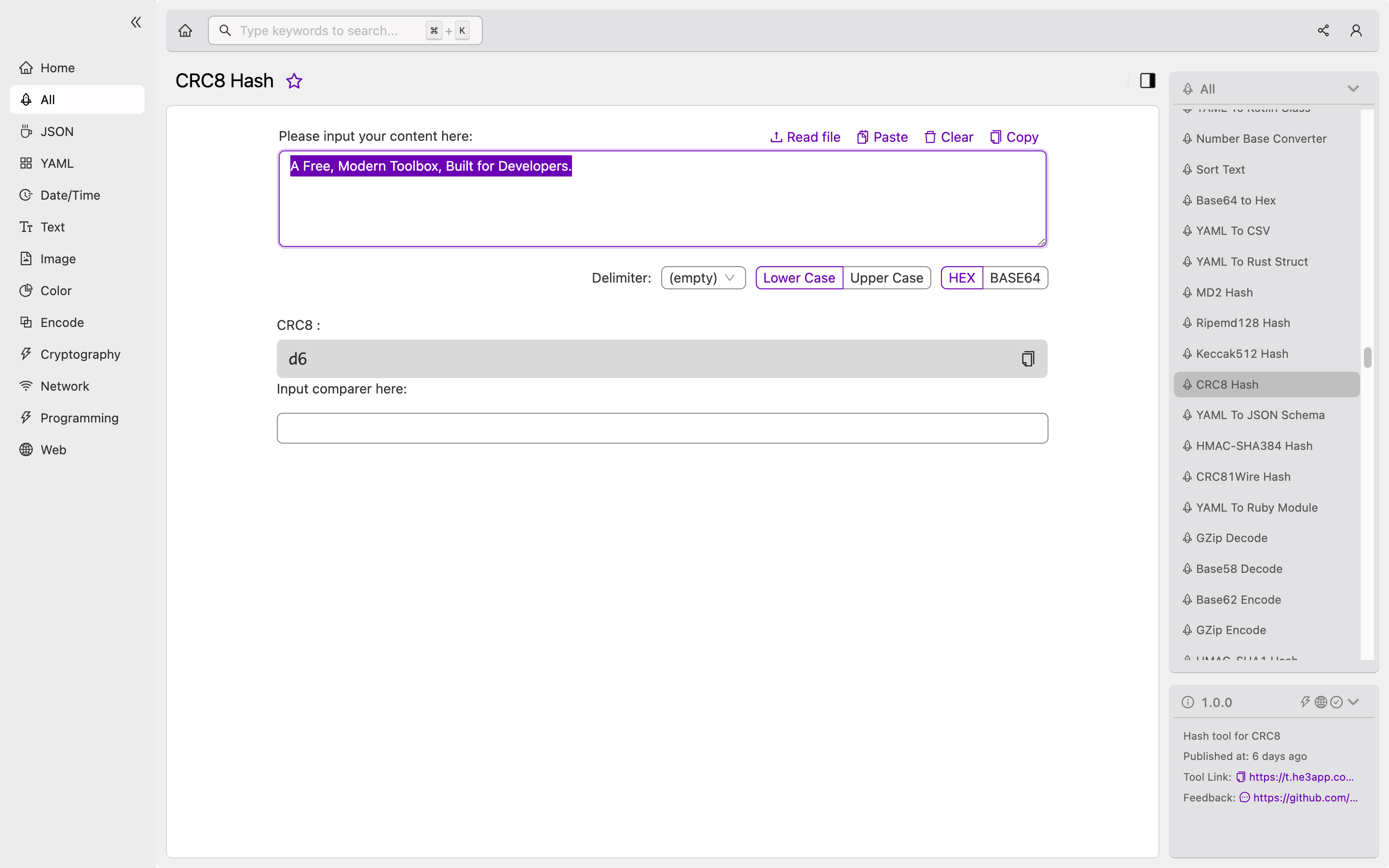
Or you can use CRC8 Hash tool in He3 Toolbox (https://t.he3app.com?hwdd ) easily.
Key Features
CRC8 Hash offers several key features that make it a popular choice for data integrity and error detection purposes, including:
-
Fast and efficient: CRC8 Hash is a computationally efficient algorithm that can perform checksum calculations quickly, even for large amounts of data.
-
Fixed-size checksum: The CRC8 Hash algorithm generates a fixed-size checksum of 8 bits, which makes it suitable for applications that require a small and fixed-size data structure.
-
Low collision rate: The probability of two different input data generating the same CRC8 Hash checksum is low, which means that the algorithm has a low collision rate.
-
Easy to implement: CRC8 Hash is a simple and easy-to-implement algorithm that can be easily integrated into different programming languages and platforms.
Scenarios of Use
CRC8 Hash can be used in various scenarios where data integrity and error detection are critical. Some examples include:
-
Network communication: CRC8 Hash can be used to verify the integrity of data packets transmitted over a network, such as Ethernet, Wi-Fi, or Bluetooth.
-
Storage systems: CRC8 Hash can be used to detect errors in stored data, such as files, databases, or memory.
-
Embedded systems: CRC8 Hash can be used in embedded systems, such as microcontrollers or sensors, to ensure the accuracy and reliability of data measurements.
Misconceptions and FAQs
Misconception: CRC8 Hash is the most secure hashing algorithm.
Fact: CRC8 Hash is not designed to be a security hashing algorithm, but rather a checksum algorithm for data integrity and error detection purposes. If security is a concern, developers should use cryptographic hashing algorithms such as SHA-256 or SHA-512.
FAQ: Can CRC8 Hash detect all types of errors in data transmission?
Answer: No, CRC8 Hash can only detect certain types of errors, such as single bit errors, but not all types of errors, such as burst errors or random errors. For more robust error detection, developers should use more advanced coding techniques, such as Reed-Solomon coding or Hamming coding.
FAQ: Can I use CRC8 Hash for data compression purposes?
Answer: No, CRC8 Hash is not designed for data compression purposes, but rather for data integrity and error detection. If data compression is required, developers should use compression algorithms, such as gzip or bzip2.
Conclusion
CRC8 Hash is a popular hashing algorithm that can be used to ensure data integrity and detect errors during transmission or storage. It offers several key features, such as fast and efficient computation, fixed-size checksum, low collision rate, and easy implementation. Developers can use CRC8 Hash in various scenarios, such as network communication, storage systems, or embedded systems. To learn more about CRC8 Hash and other CRC algorithms, visit the Wikipedia page on Cyclic Redundancy Check.
References:
