A Comprehensive Developer’s Guide to Decrypting DES: Demystifying the Process
The advent of modern computing has changed the way we store and process data. With an ever-increasing amount of sensitive information being transmitted over the internet, there is a pressing need to secure that data from prying eyes. Encryption is a fundamental technique that provides a solution to this problem, and DES (Data Encryption Standard) is one of the most widely-used encryption standards in the world. In this article, we will discuss what DES encryption is and how it works, and provide developers with practical scenarios for its everyday use.
How DES Decryption Works
DES encryption is a symmetric-key algorithm that encrypts data using a secret key using 64-bit blocks. The data is broken up into 64-bit blocks, and then each block is encrypted using the key. The encrypted blocks can then be transmitted over the internet or stored on a device. To decrypt the data, the receiver uses the same key to reverse the encryption process and recover the original plaintext data.
Here’s a sample code in Python that demonstrates how DES decryption works:
from cryptography.fernet import Fernet
key = Fernet.generate_key()
cipher_suite = Fernet(key)
cipher_text = cipher_suite.encrypt(b"Hello World")
plain_text = cipher_suite.decrypt(cipher_text)
print(plain_text.decode())
# output: Hello WorldIn this example, we first generate a secret key using the cryptography library’s Fernet class. We then create an instance of the Fernet class using the key, which we can use to encrypt and decrypt data. Finally, we use the decrypt method to recover the plaintext data.
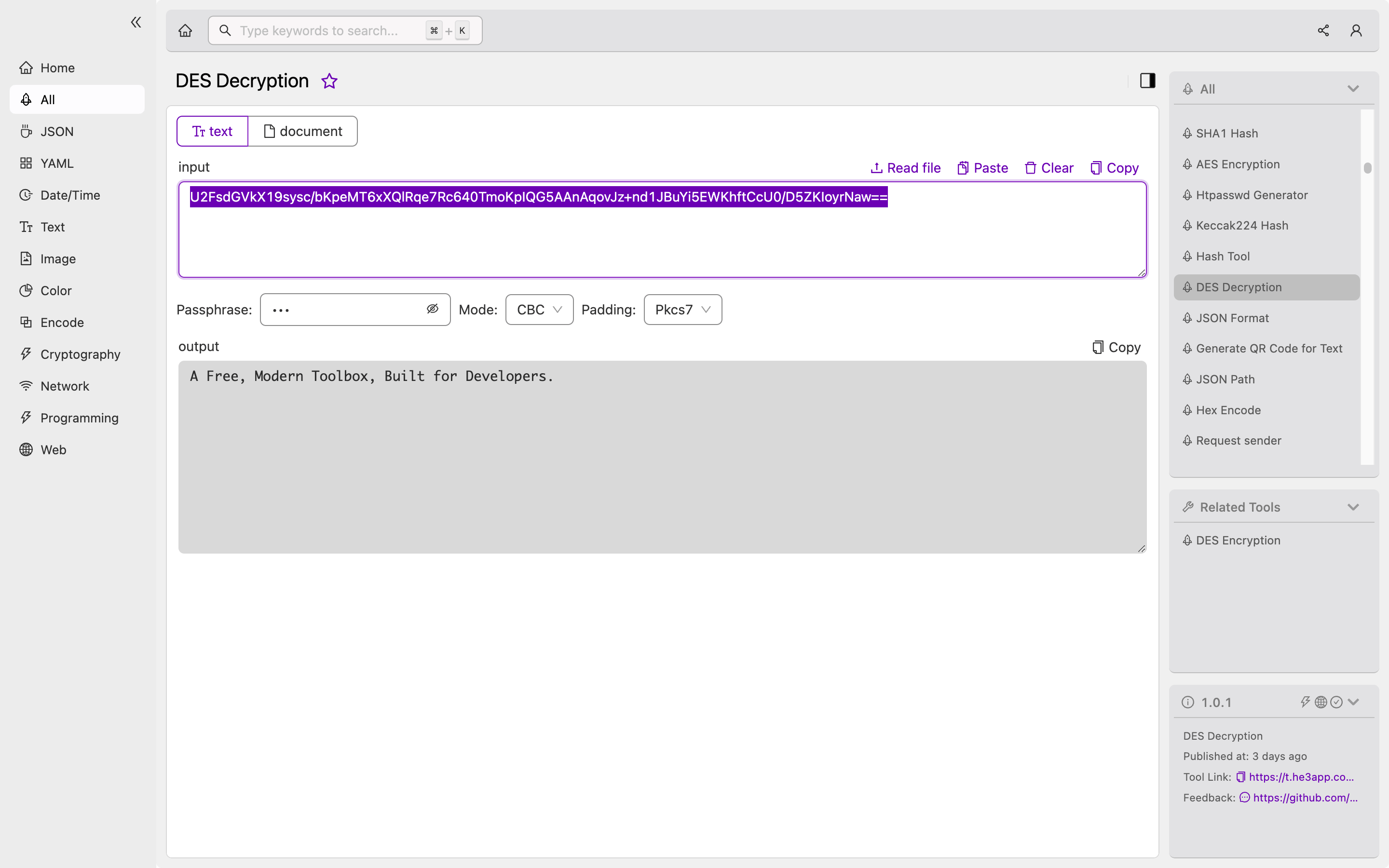
Or you can use Des Decryption tool in He3 Toolbox (https://t.he3app.com?o2yp ) easily.
Practical Scenarios for Developers
DES decryption finds use in a variety of settings where sensitive data needs to be secured, including:
Authentication
Authentication is a central aspect of many applications, and often involves the exchange of sensitive information over the internet. Encrypting this data using DES encryption can provide an added layer of security and make it harder for attackers to steal login credentials.
Secure Storage
Storing sensitive data on disk poses a security risk, as it can be accessed by anyone with physical access to the device. DES encryption can be used to encrypt the data before storing it on disk, providing protection against unauthorized access.
Secure Communications
Transmitting sensitive data over the internet poses a significant security risk, as attackers can intercept and eavesdrop on the data. Encrypting the data using DES encryption can protect it from unauthorized access and ensure that it can only be read by the intended recipient.
Key Features of DES Decryption
| Feature | Description |
|---|---|
| Symmetric-key algorithm | Data is encrypted and decrypted using the same secret key. |
| 64-bit blocks | Data is broken up into 64-bit blocks for encryption. |
| Widely-used standard | The DES encryption standard is widely-used and tested for security. |
| Relatively fast | DES encryption and decryption operations can be carried out relatively quickly. |
Misconceptions and FAQs
Isn’t DES Decryption Obsolete?
While DES decryption is an older encryption standard, it is still widely-used and provides robust security for most applications. However, it is important to note that DES encryption is vulnerable to certain forms of attack, such as brute-force attacks. As such, more modern encryption standards such as AES (Advanced Encryption Standard) should be used for highly-sensitive applications.
Is DES Decryption Easy to Implement?
Implementing DES decryption can be challenging, as it requires a deep understanding of cryptographic techniques and standards. However, libraries such as the cryptography module in Python make it relatively easy to implement DES decryption operations in your applications.
Conclusion
DES decryption is a fundamental encryption technique that provides an added layer of security for applications and data. Its symmetric-key algorithm and wide usage make it a popular choice for developers looking to secure their applications, store sensitive data on disk, or transmit data over the internet. By implementing DES decryption in your applications, you can help protect your users’ data from malicious attackers.
References
