Introduction
With the increasing importance of secure data transfer and communication, developers rely on encryption algorithms to secure their applications from malicious attacks. SM2 Encryption is a widely used encryption algorithm that has found its way into various applications. This article provides an overview of SM2 Encryption, its key features, and how it works.
What is SM2 Encryption?
SM2 Encryption is a symmetric key encryption algorithm that is widely used in cryptography. It is a Chinese encryption standard that is based on the elliptic curve cryptography (ECC) algorithm. SM2 Encryption is an extension of the SM1 Encryption algorithm, which is designed for symmetric encryption.
How Does SM2 Encryption Work?
SM2 Encryption uses the elliptic curve cryptography (ECC) algorithm and the Chinese Remainder Theorem to secure data transfer and communication. Here is a step-by-step guide on how SM2 Encryption works:
- Generate a private key and a public key using the ECC algorithm.
- Generate a symmetric key and encrypt the data using the symmetric key.
- Encrypt the symmetric key using the public key generated in step 1.
- Send the encrypted data and the encrypted symmetric key to the receiver.
- The receiver decrypts the symmetric key using its private key and then uses the symmetric key to decrypt the message.
Here is the sample code to generate the private key and public key using OpenSSL:
openssl ecparam -name sm2p256v1 -genkey -out sm2key.pem
Key Features of SM2 Encryption
Here are some key features of SM2 Encryption:
- SM2 is a widely accepted encryption standard in China and is used in various applications, including mobile payments and digital signatures.
- SM2 is based on the elliptic curve cryptography (ECC) algorithm, which is more secure than other encryption algorithms.
- SM2 supports key sizes of 128, 192, and 256 bits.
- SM2 Encryption is faster than other encryption algorithms, such as RSA.
Scenarios of Using SM2 Encryption for Developers
Here are some scenarios where developers can use SM2 Encryption:
- Mobile payments: Developers can use SM2 Encryption to secure mobile payment transactions.
- Digital signatures: Developers can use SM2 Encryption to generate digital signatures that can be used to verify the authenticity of documents and messages.
- Secure communication: Developers can use SM2 Encryption to secure data transfer and communication between two parties.
Misconceptions about SM2 Encryption
Some misconceptions about SM2 Encryption include:
- SM2 Encryption is only used in China: While SM2 Encryption is a Chinese encryption standard, it is also used in various other countries.
- SM2 Encryption is less secure than RSA: SM2 Encryption is based on the ECC algorithm, which is considered to be more secure than RSA.
FAQs
Here are some FAQs about SM2 Encryption:
-
Is SM2 Encryption free to use? Yes, SM2 Encryption is a free and open-source encryption algorithm.
-
Can SM2 Encryption be cracked? No, SM2 Encryption is a secure encryption algorithm that is based on the ECC algorithm.
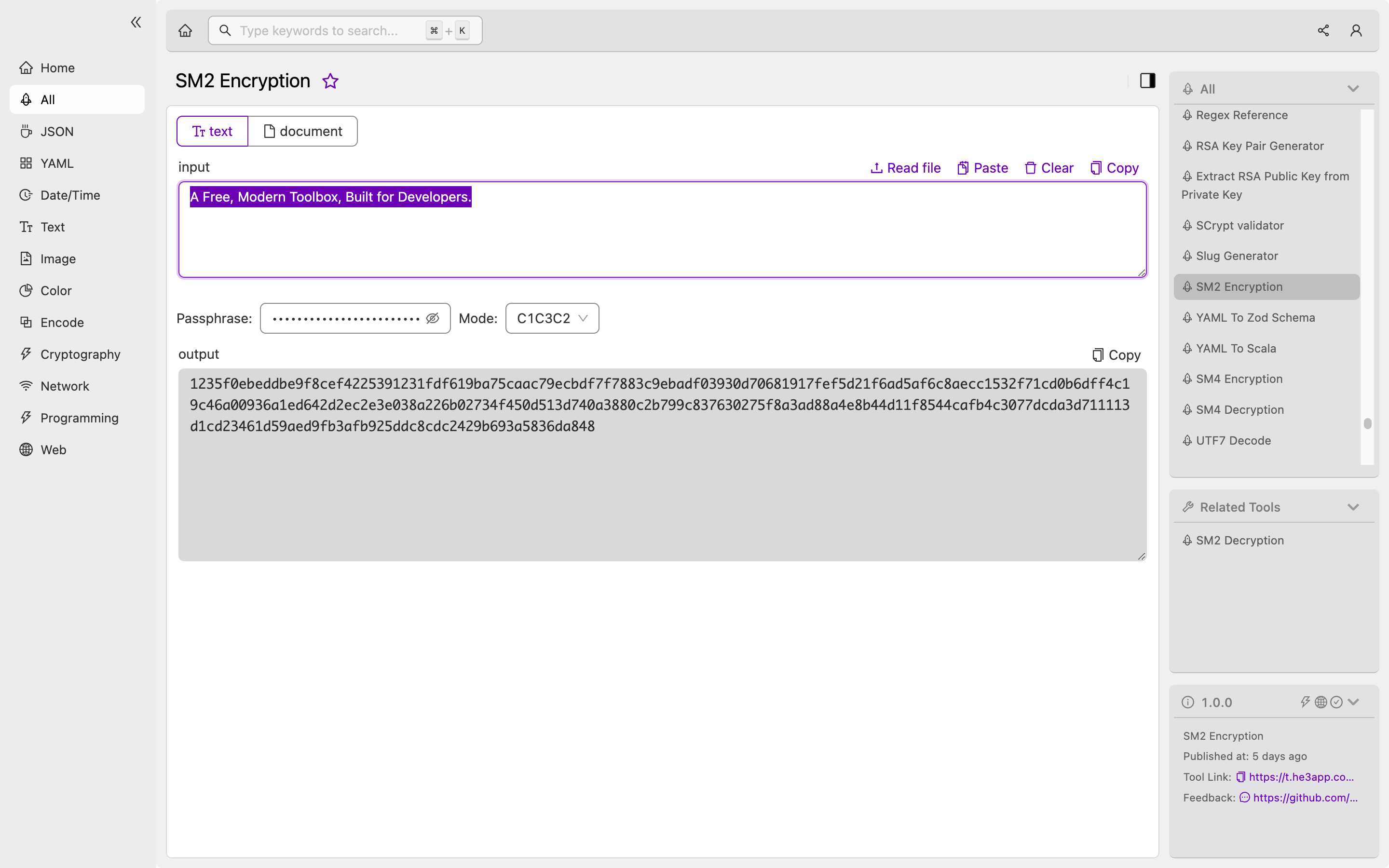
How to Use SM2 Encryption
To use SM2 Encryption, you can use the SM2 Encryption tool in He3 Toolbox (https://t.he3app.com?9bay ) easily.
Conclusion
SM2 Encryption is a widely used encryption algorithm that provides secure data transfer and communication. Its key features, such as the use of the ECC algorithm and support for key sizes of 128, 192, and 256 bits, make it a popular choice among developers. By understanding how SM2 Encryption works and how it can be used, developers can implement secure communication in their applications.
