Introduction
In software development, data integrity is crucial in ensuring that data is not lost or corrupted during transmission or storage. This is where hash functions come in, as they generate a unique value (a hash) from the input data, which can be used to verify its integrity. One such hash function is CRC81Wire Hash, which is widely used in various applications.
What is CRC81Wire Hash?
CRC81Wire Hash is a hash function that generates a 256-bit hash value from an input data of any length. It uses the Cyclic Redundancy Check (CRC) algorithm, which involves dividing the input data into fixed-size chunks and performing mathematical operations on each chunk to generate the final hash value.
How does it work?
The CRC81Wire Hash algorithm works by first initializing a 256-bit hash value to a predetermined value. It then divides the input data into fixed-size chunks and performs mathematical operations on each chunk. These operations involve performing XOR, shifts, and multiplication by a predefined constant. The final hash value is obtained by XORing the initial hash value with the result of the operations performed on the input data.
Here’s a sample Python code that demonstrates how to use CRC81Wire Hash:
import crcmod
hash_func = crcmod.predefined.mkCrcFun('crc-256')
data = b'This is a sample input data'
hash_value = hash_func(data)
print(hash_value.hex())This code uses the crcmod library in Python to generate the CRC81Wire Hash value of a sample input data.
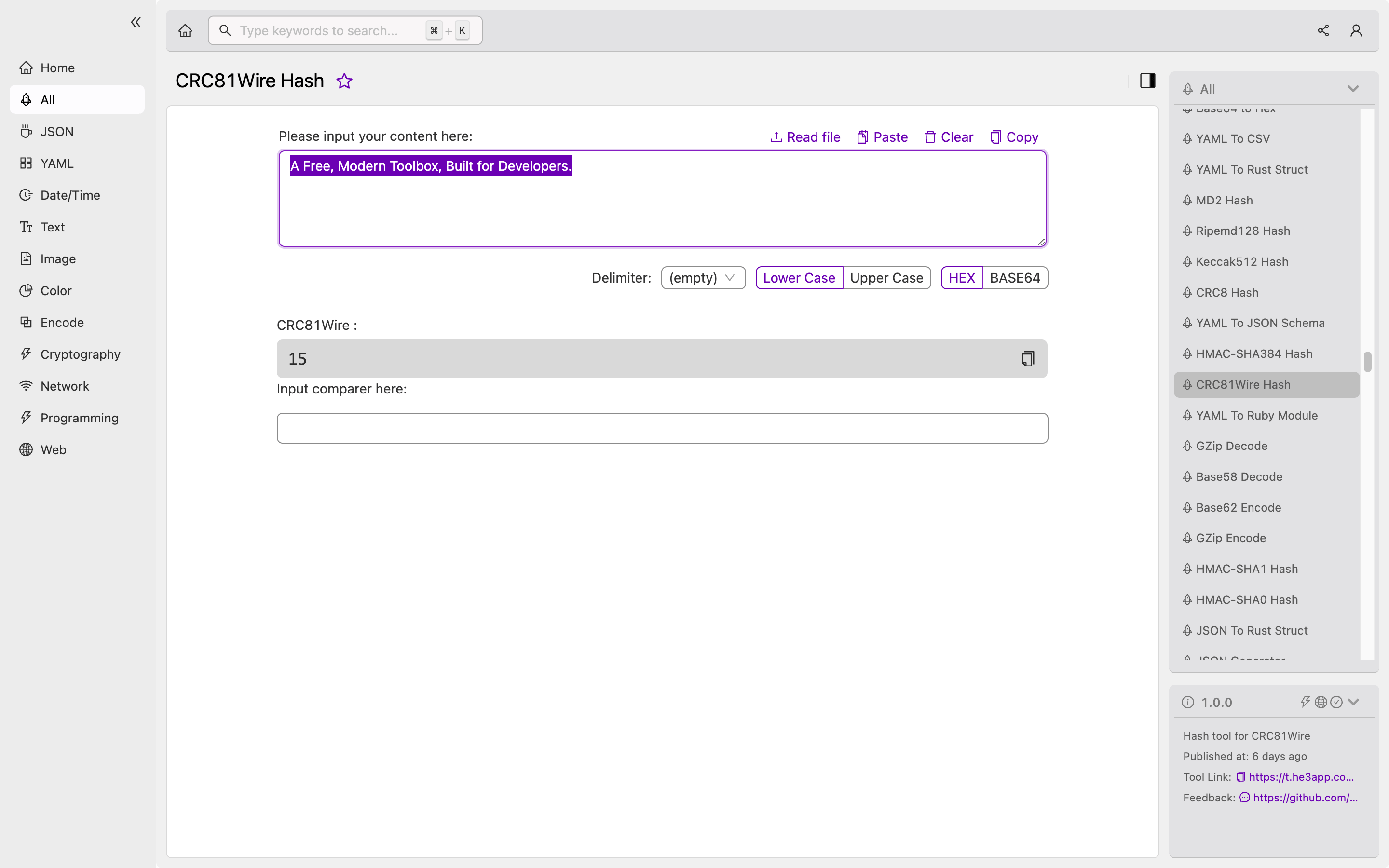
Or you can use CRC81Wire Hash tool in He3 Toolbox (https://t.he3app.com?8dqr ) easily.
Key features
Here are some key features of CRC81Wire Hash:
- Generates a 256-bit hash value from an input data of any length
- Uses the CRC algorithm for efficient processing of input data
- Widely used in various applications for data integrity and security
Scenarios for Developers
As a developer, you may encounter different scenarios where you need to use CRC81Wire Hash. Here are some examples:
- In data transmission applications, you can use CRC81Wire Hash to ensure that the data sent is not lost or corrupted during transmission.
- In data storage applications, you can use CRC81Wire Hash to verify the integrity of stored data.
- In cryptography applications, you can use CRC81Wire Hash as part of a larger encryption scheme to add an additional layer of security.
Misconceptions
One common misconception is that CRC81Wire Hash can be used for encryption. However, this is not the case, as hash functions only generate a fixed-length value from the input data and cannot be used to reverse-engineer the original input data. Another misconception is that two different input data cannot have the same hash value (a collision). While it is rare, collisions can occur in hash functions.
FAQs
-
Is CRC81Wire Hash secure enough for data security? CRC81Wire Hash is a widely used hash function for data integrity and security. However, it is not recommended to use it as the sole security measure. For stronger security, you should use a combination of hash functions and encryption algorithms.
-
Can CRC81Wire Hash be used for password storage? No, CRC81Wire Hash is not recommended for password storage, as it is not secure enough. For password storage, you should use a dedicated password-hashing algorithm, such as bcrypt or Argon2.
Conclusion
CRC81Wire Hash is an essential hash function that provides data integrity and security in various applications. Understanding how it works and how to use it is crucial for developers working with data transmission, storage, and cryptography applications. To learn more about CRC81Wire Hash and other hash functions, you can check out the following references:
