Extract RSA Public Key from Private Key: A Guide for Developers
If you are a developer working with RSA encryption, you may need to extract the public key from the private key for various reasons, such as key management or certificate creation. This guide will explain the concept and process of extracting RSA public key from the private key and provide example code and scenarios for developers.
What is RSA Public Key and Private Key?
RSA (Rivest-Shamir-Adleman) is a widely used encryption algorithm in cryptography. It uses two keys, a public key and a private key, to encrypt and decrypt data. The public key is used by anyone who wants to send encrypted data to the owner of the private key. The private key is kept secret by the owner and used to decrypt the received data.
How to Extract RSA Public Key from Private Key?
To extract the RSA public key from the private key, you can use various programming languages, libraries, or command-line tools. Here is an example code in Python using the cryptography library:
from cryptography.hazmat.primitives import serialization
with open("private_key.pem", "rb") as key_file:
private_key = serialization.load_pem_private_key(
key_file.read(),
password=None
)
public_key = private_key.public_key()
pem_public_key = public_key.public_bytes(
encoding=serialization.Encoding.PEM,
format=serialization.PublicFormat.SubjectPublicKeyInfo
)
with open("public_key.pem", "wb") as key_file:
key_file.write(pem_public_key)This code loads the private key from “private_key.pem” file, extracts the public key from it, and saves it in “public_key.pem” file. You can also use command-line tools like OpenSSL to extract the public key from the private key.
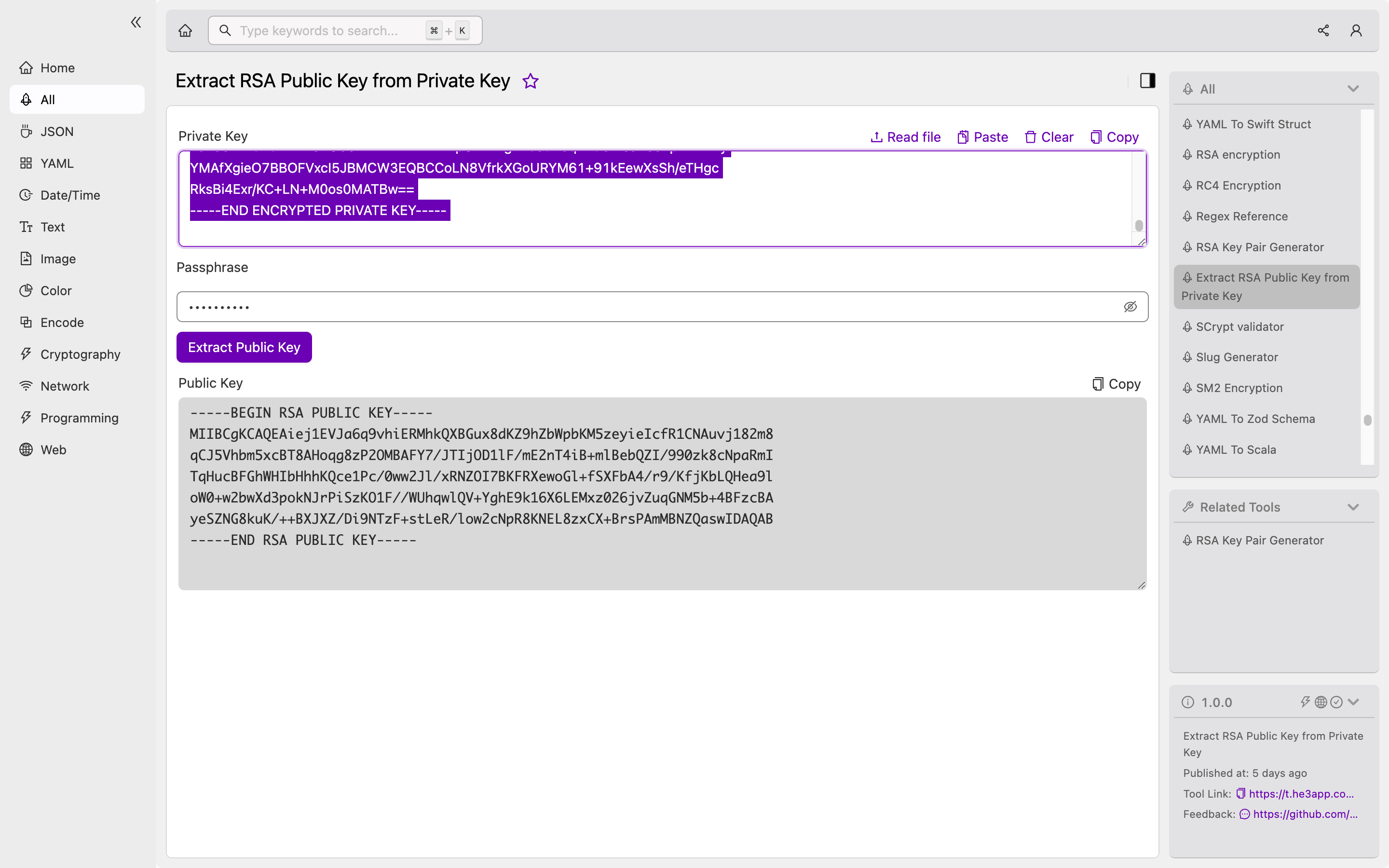
Or you can use Extract RSA Public Key from Private Key tool in He3 Toolbox (https://t.he3app.com?218j) easily.
Scenarios for Developers
Extracting RSA public key from private key can be used in various scenarios, such as:
- Key management: You may need to extract the public key from a private key to share it with others who need to send encrypted data to you.
- Certificate creation: To create an SSL certificate, you need to generate a key pair and extract the public key to create a certificate signing request.
Key Features
Here are some key features of RSA encryption and key extraction:
| Feature | Description |
|---|---|
| Asymmetric encryption | RSA encryption uses two different keys for encryption and decryption. |
| Secure communication | RSA enables secure communication between two parties by encrypting the data with the recipient’s public key and decrypting it with the recipient’s private key. |
| Extracting public key | Extracting the RSA public key from a private key can be useful in various scenarios, such as key management and certificate creation. |
Misconceptions and FAQs
Do I need the private key to decrypt data encrypted with the public key?
No, the private key is only used to decrypt data encrypted with the corresponding public key. If you want to decrypt data encrypted with a public key, you need to have the private key that matches the public key.
Can I generate the public key from scratch without the private key?
No, the public key is derived from the private key, so you need the private key to generate the public key.
Conclusion
Extracting RSA public key from private key is a useful process for developers working with RSA encryption. This guide explained the concept and process of extracting the public key, provided example code and scenarios, and highlighted some misconceptions and FAQs. You can easily extract the public key using various programming languages, libraries, or command-line tools.
Reference links:
